My first cyber-security/hacking related con this year happened to be Insomni'hack last week (I'm currently planning to visit a bunch of cons so I can travel, learn, network and meet new friends). It's a Swiss cybersecurity conference and contest in Lausanne (french part of Switzerland), so i happened to say "mon francais ce n'est pas tres bon" a lot of times.
Overview
| Criteria | Rating | Desc |
|---|---|---|
| Vibe | 2/5 | Felt mostly corporate, had some cool parts (lockpicking, some talks) |
| Talks | 4/5 | The ones I visited, I liked -> But I went for more technical ones except for one |
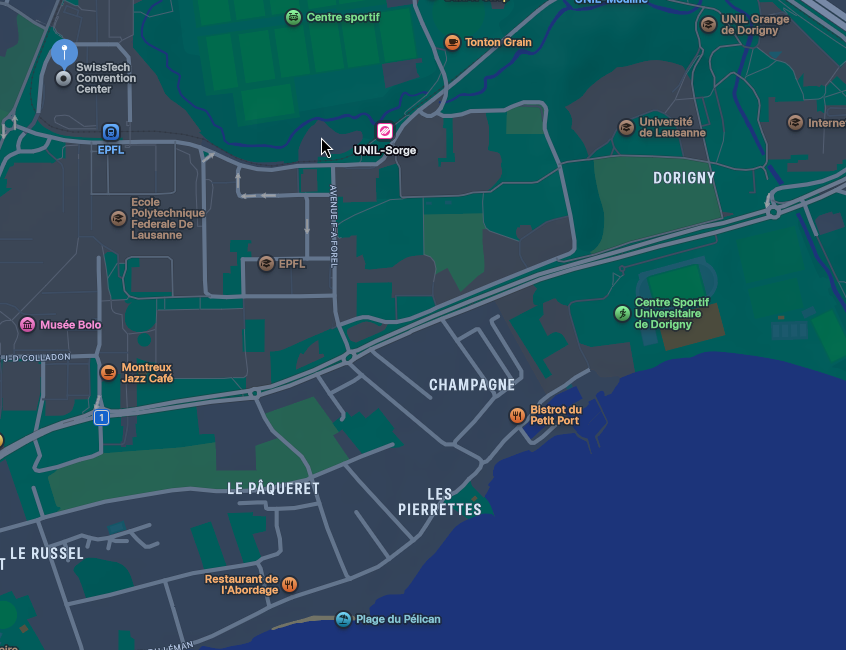
| Location | 4/5 | The location is a couple of stations away from the lake (with a cool skatepark) and is right at a metro station (next to the EPFL). There is restaurants and grocery stores literally next to it (like a 1 min walk). Easily reached by skateboard :3 |
| Premises | 3/5 | Nothing really special. A 3 Level conference center. AC, 3 different talk-rooms. Rooms had built-in tables into chair and it felt like you got a nice view from most of the seats. |
| Schedule | 2/5 | First 3 days were workshops, last two days mostly talks. Conference day was from 9AM to 6PM, which I guess is an usual working day. I rather prefer the CCC way. |
| CTF | 4/5 | Had some hiccups, but was super fun. Was playing mostly for fun tho |
| CTF Team | 5/5 | Met the team at the conference and joined <3 was super fun |
| Food | 1/5 | Didn't get to check it out, since most of it wasn't vegan |
| Workshops | N/A | Missed them |
The arrival - Wednesday 18th March 2026
I arrived the day before the conference at my hotel around midnight. The staff was kind enough to add a picture of Pedro Pascal next to my bed as I requested :3

I also matched with a cool person on an app and made plans for after the con on Thursday.
First Day of Con - Thursday 19th March 2026
After showing my ticket and checking out the premises I decided to head down to the "basement"/garden area. It was filled with company expo stands with some merch/swag like pens and stuff next to the coffee and snack section. Sadly most of the food (except for bananas and apples) weren't vegan. So all i had was coffee.
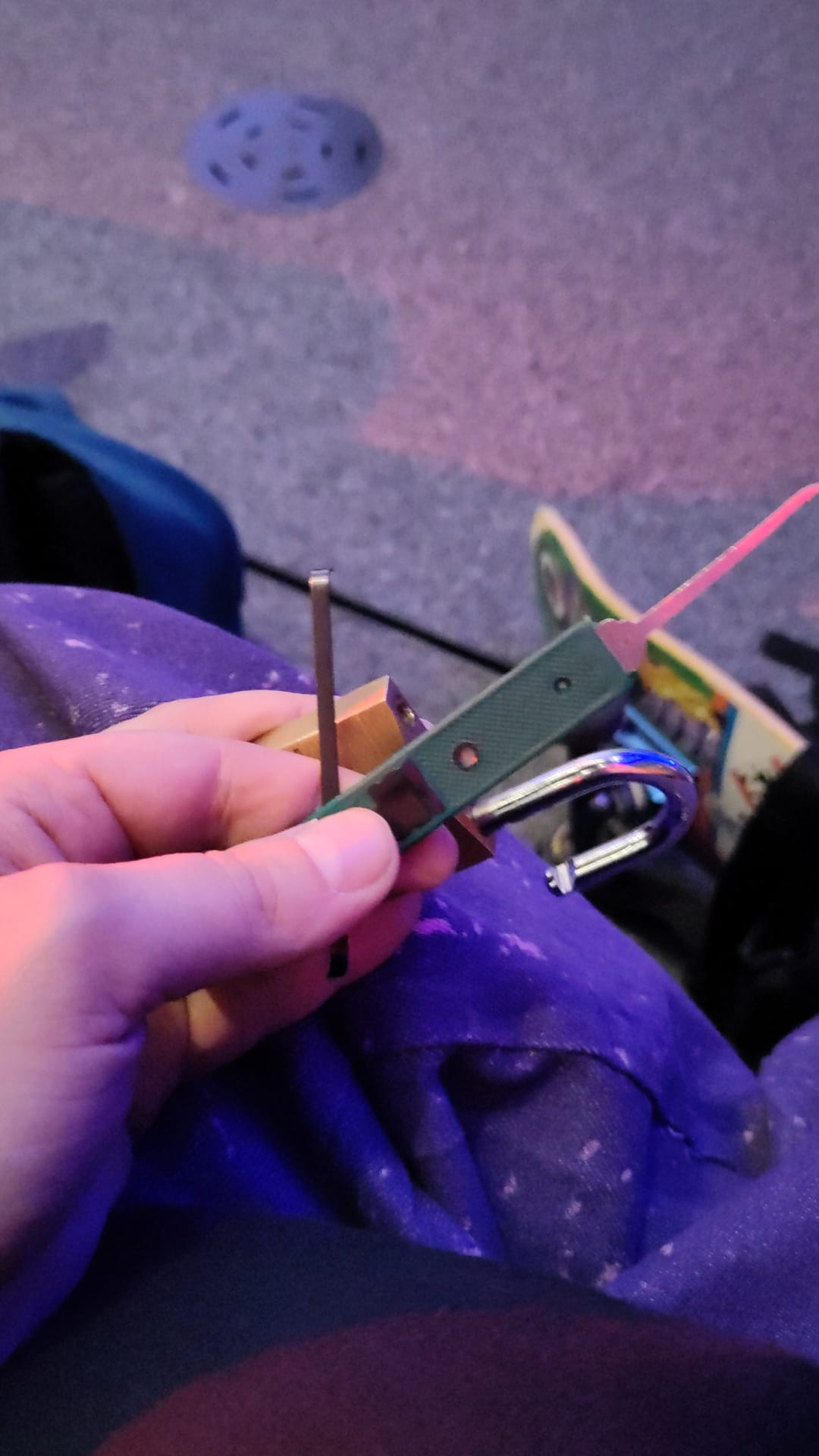
Lockpicking
However the most fun part was the lockpicking stand. Remy quickly explained to me how it works and I got to practice on some smaller/niche locks before he gave me a real one. I was able to take the lock and tools with to the talks to fidget with them during the talks.
"Weird" CISO talk
The first talk I visited was by Oliver Martinet the CISO of TX Group. One of the biggest Media/"journalism" corpos in Switzerland. They're the ones behind 20min (the news) - one of the worst news outlets bordering on propaganda paper, in my humble opinion. The talk was called "Other CISOS say we made very weird choices in our Cyber Security. Of Course we did!".
The talk was mostly about not caring to fulfill compliance requirements (since a media business doesn't have the same level of compliance requirements as a bank), and how they can allow their journalist to be happy and productive and free (like i.e. accessing the dark web from the company network).
Coffee break
The talk was followed by a coffee break.
 At the lock picking stand I met a fellow transfem person and we got to chat a lil bit - She ended up inviting me to her all transfem CTF team for the next day and I was super happy! I wasn't expecting to find such a cool team so easily and fast :3
At the lock picking stand I met a fellow transfem person and we got to chat a lil bit - She ended up inviting me to her all transfem CTF team for the next day and I was super happy! I wasn't expecting to find such a cool team so easily and fast :3
Hacking Context Menus
The next talk I visited was called "Shift Happens: Uncovering two built-in command injections in Windows context menus" (Why is every talk title a paragraph now).
The talk focused on getting a RCE (or at leas a Code Execution) by naming a folder in Windows 10/11 weirdly (mostly use special signs and spaces). It also showed some real world abuse scenarios.
It was held by (yet another) Remi. A Senior Security Researcher at a french cyber security company.
SAP hacking
I sadly can't say a lot about the "Improving SAP security: tooling for authorizations and post-exploitation" talk, because I kept zoning out and was thinking about the meetup after the con.
After the Con-Day - Thursday 19th March 2026
After the con I went for a stroll by the lake towards the skate park where me and Malon (name changed for privacy reasons) decided to meet up. I snapped a nice pic on my way there:
 We skated at the park, talked a lot, went to dinner together and then walked/skated around the deserted EPFL campus (Malon had an E-Scooter and I a Skateboard, so I held on to her while she was going super fast :3) and ended up in a student bar.
We skated at the park, talked a lot, went to dinner together and then walked/skated around the deserted EPFL campus (Malon had an E-Scooter and I a Skateboard, so I held on to her while she was going super fast :3) and ended up in a student bar.
It was super nice, we cuddled on a couch while she had a beer and I had a syrup :D The night ended with us sharing a metro-ride in the same direction until I had to get off.
Oh, and it turns out that Malon knew the CTF team I was going to join the next day, lol.
2nd Con-Day - Friday 20th March 2026
During the second day I visited more interesting talks. The more tech-related talks seemed to be in Campus or Cloud (room names). My favorite room was the Cloud-Room. It felt more like a hacker/community vibe in there. Also the talk topics reflected that.
SAMSUNG S25 RCE
I visited a talk of two speakers that were trying to find a vulnerability for pwn2own. "Shoot for the Galaxies: Our Samsung S25 1-click RCE Journey" was the name. They told their story of finding exploits via the "Android sync" app.
In the end, through a chain of vulnerabilities (like missing encryption/signatures, bypassing PINs/Logins, etc...) they were able to install and launch arbitrary APKs on the S25 with a single tap.
Sadly that was already too late for Pwn2Own.
Keyboards as targets
One of the most fun and interesting talks was "Keypocalypse" (FINALLY AN ACTUAL TITLE AND NOT A PARAGRAPH!).
Emilien Le Jamter explained how mechanical keyboards (or more specifically their OS) can be abused to create a nice, undetectable keylogger. The Keylogger would be installed directly on the OS of the mechanical keyboard (which is open source and can be changed).
The OS would be installed by the user via phishing and since the keylogger is on the hardware, if an employee brings their keyboard to work, it'll work there too. The talk included threat modeling, supply chain attacks, firmware extraction, etc...
I was hoping the talks would be available online, but I can't seem to find em.

IDEs as attack vectors
The talk "From Code to Compromise: Turning modern day IDEs into attack vectors via malicious Extensions" (back to paragraphs) showcased how you could spoof malicious VS Code Extensions to look like real ones.
Debjeet Banerjee showed real-life cases where this was done, but also showed us how you could do it yourself :P
This is the talk were I really, really wished they would have recorded it and put it online to see, but maybe that can be a feedback for the organizers.
PS: picked the next lock during this talk

Ransomware Movie
I went to a movie showing of a movie called "Don't go to the police" thinking it would be cool, but instead it was just a movie about an (old) ransomware attack. They had cool swag tho -> A bamboo power bank.
The CTF - 20th to 21st March 2026
The highlight of the conference was the on-site CTF. After the movie showing I went up to the CTF room to find some of my teammates already there. After introducing ourselves I started setting up my laptop to be ready for the CTF, got some drinks/snacks and skated a bit in front of the conference center.
The CTF was super fun - I started out on a challenge on my own and was joined by two others after a while. I found an SQLi attack vector on the website, but couldn't figure out the complete SQLi Query to get the Flag. Together we were able to solve it.
But my favorite challenge was "the quest". We first had to get access to the source code of a game, which contained a secret encoded message with the PIN of the "Arcade"-Box near the stage with the NFC tags. On those tags you needed to put on coins so you could go and play the game.
It was very fun to play it with Frezlotte. She also uses noctalia-shell, yayyyyyyy. Until I went home I was mostly going around our team and helping/rubber ducky-ing the rest of the team, took a short skating break and got to know the group a lil better.
I tried to take a selfie while skating but fell during it:
Worth it?
Mostly for the CTF yes, I can't say how the workshops are - but they do cost more money (i think around 1k or even more!). The talks are a mix of more corpo-focused and tech-focused topics, the food sadly has not a lot of vegan options, but the lock-picking table (which also hosted a competition) was super fun.
I would go again mostly cuz I enjoyed the location, the CTF and the ppl I met there - and hope to see them again next year (at least, would also like to meet again before that lol) <3.
